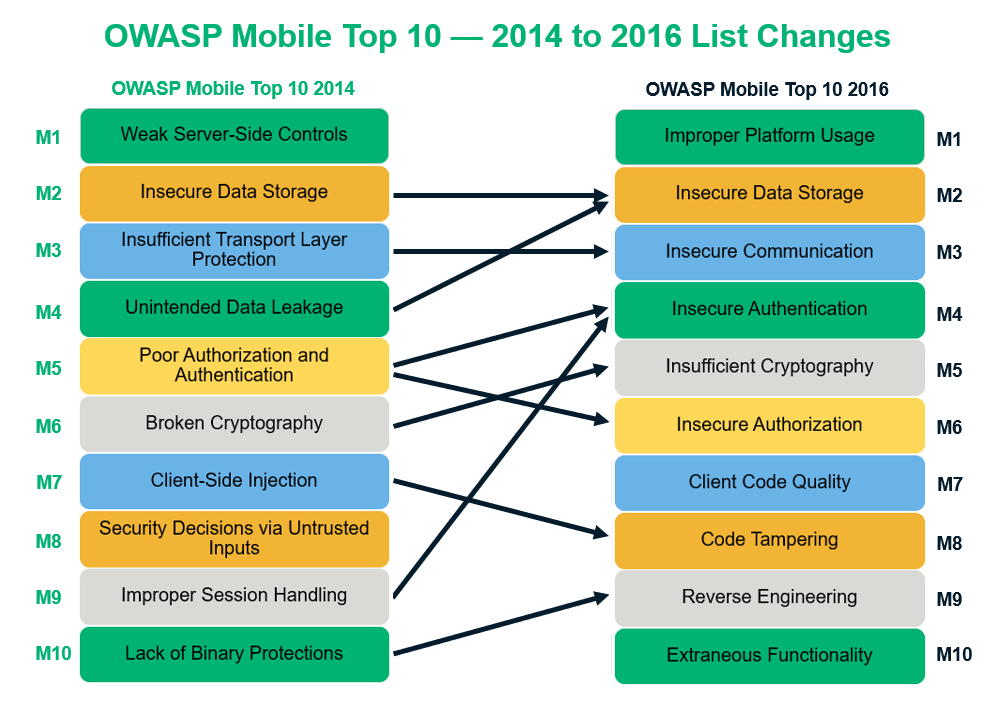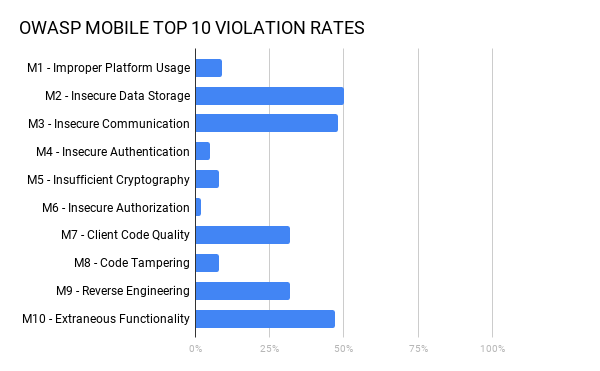
OWASP mobile top 10 security risks explained with real world examples | by Kristiina Rahkema | The Startup | Medium
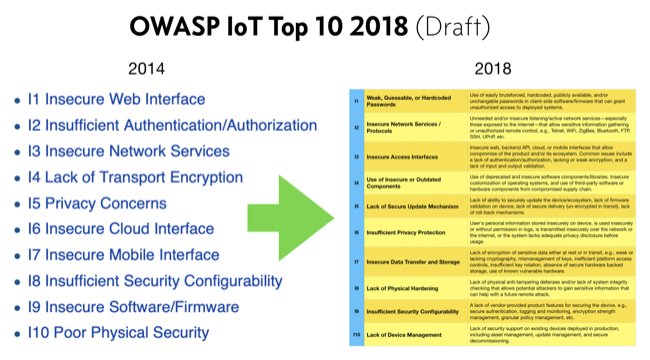
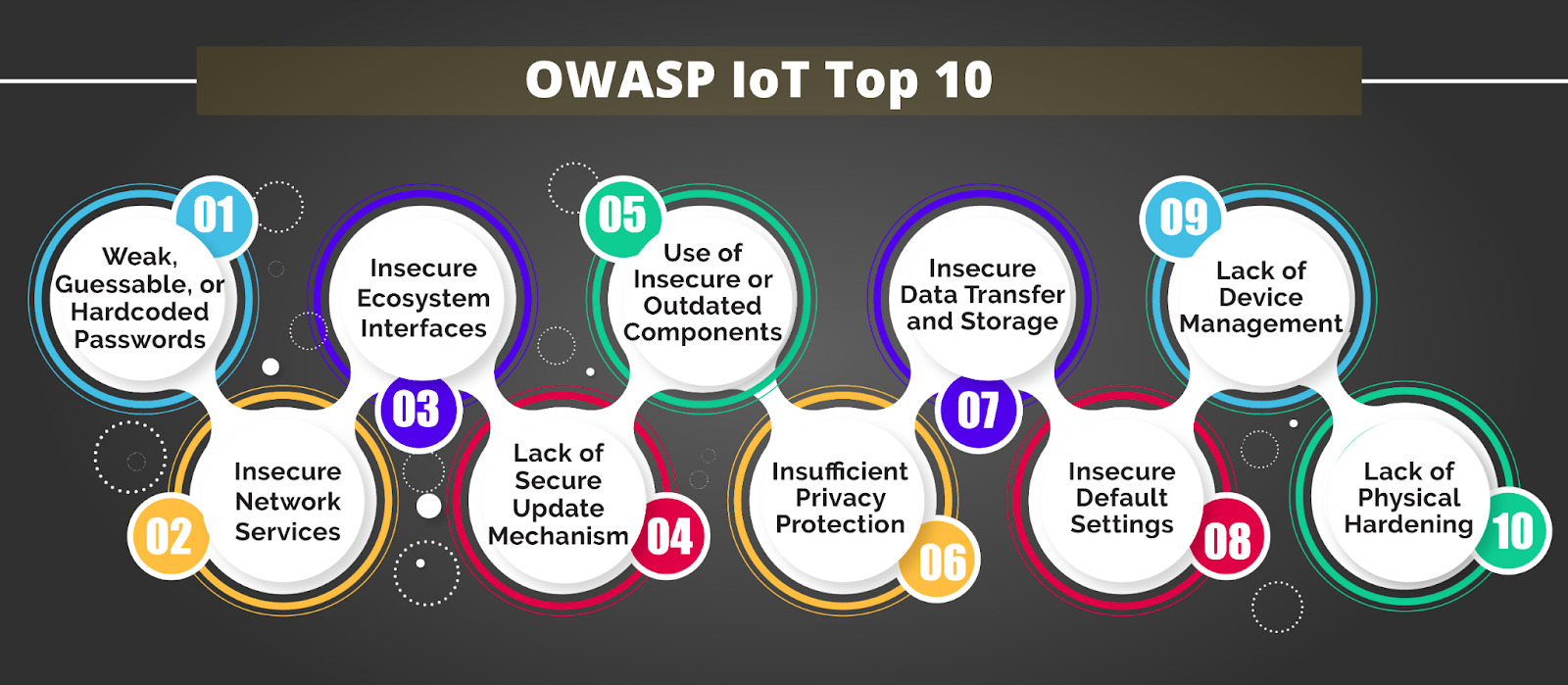
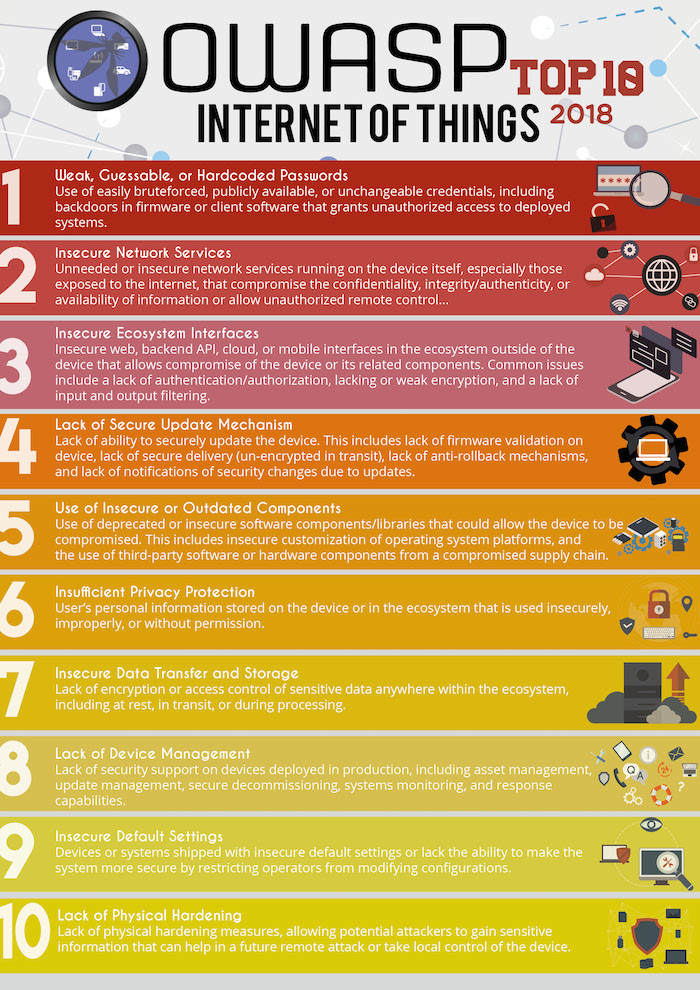
Neira Jones on Twitter: "Preparing to Release the #OWASP #IoT Top 10 2018 https://t.co/cCSmVTmtBB #infosec #appsec #DevSecOps @owasp https://t.co/2WaPcvn4A5" / Twitter